Summary
DISCLAIMER: This module requires access to a macOS machine for completion. Refer to the end of this page for more details.
macOS is a staple in many environments and businesses, such as academia, content creation, and audio/visual shops worldwide. Furthermore, macOS makes for an excellent pentesting OS and is very popular among pentesters and developers alike, for its security and ability to natively run pentesting tools as well as simulate other OS's through virtual machines.
Understanding how to navigate the file system and the command line is essential for effective enumeration, privilege escalation, lateral movement, post-exploitation, and defense. When set up correctly, we can even use macOS as our attack box during assessments. With advances in centralized administration, we are starting to see macOS hosts within Active Directory environments as well more frequently. This module covers the essentials for starting with the macOS operating system and command line.
This module will provide a quick history lesson on the origins of macOS and its architecture and then guide us through utilizing and administering all it has to offer. We will practice using the Graphical User Interface (GUI) along with the Command-line Interface (CLI) to administer many different portions of the host, including:
- System settings and preferences
- Filesystem navigation and usage
- Networking concepts as they pertain to macOS
- Application and update control via native apps and the use of Homebrew
- Security considerations to include host hardening and monitoring
Furthermore, this module will cover the following:
- macOS system structure
- File system specifics
- Permissions management
- macOS services and applications
- Interacting with the operating system (CLI & GUI)
- Security Considerations
- Application management
This module is broken down into sections with accompanying hands-on exercises to practice the tactics and techniques we cover.
You can start and stop the module anytime and pick up where you left off. There is no time limit or "grading," but you must complete all of the exercises and the skills assessment to receive the maximum number of cubes and have this module marked as complete in any paths you have chosen.
The module is classified as "Fundamental" and assumes that the student has a basic knowledge of the macOS operating system from a casual user perspective.
To complete this module, you must have access to a macOS machine (e.g., MacBook/Mac Mini/Mac Pro). If you do not have access to a Mac, you may still take the module and go through it to understand the macOS fundamentals, though you will not be able to practice the provided exercises within the module. Furthermore, the module may require basic terminal usage, mostly covered in the Linux Fundamentals module, so we recommend doing that module before this one.
What Is macOS?
Many have and use an Apple product in their lives every day. From your Macbook to your iPhone or iPad, there are many different revisions to the Apple OS line, but most of them are, in fact, based on macOS (originally Mac OS X). So let's answer the question, "What is macOS?"
Let's start this module by breaking down the history of macOS, its use, architecture, and core components. macOS is the official term for the operating system used on Apple computers. It is a widely used OS and is second in market use only to Windows operating systems. It can be found in the realms of daily home use, business management, graphical design, and arts.
History Roundup
Let's take a look at the origins of macOS for a minute.
Timeline
2000-2002
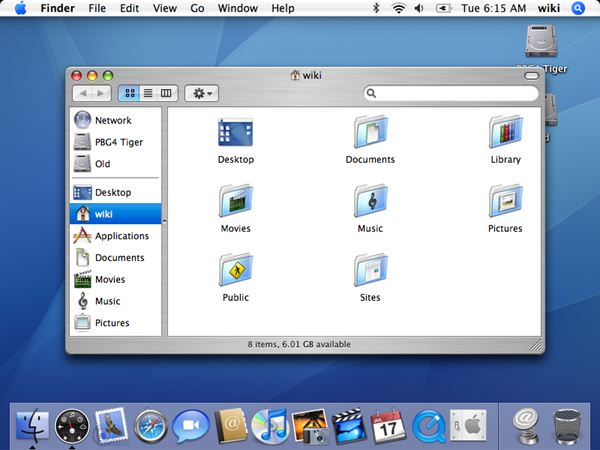
This is known as the original start to OS X leading up to macOS as we know it. In the fall of 2000, Apple released a public beta code named Kodiak for users to test and provide feedback. After taking in those responses and making fixes, Apple released Mac OS X (10.0), named Cheetah, in the spring of 2001. This is the first time the world will see the new User interface Aqua. 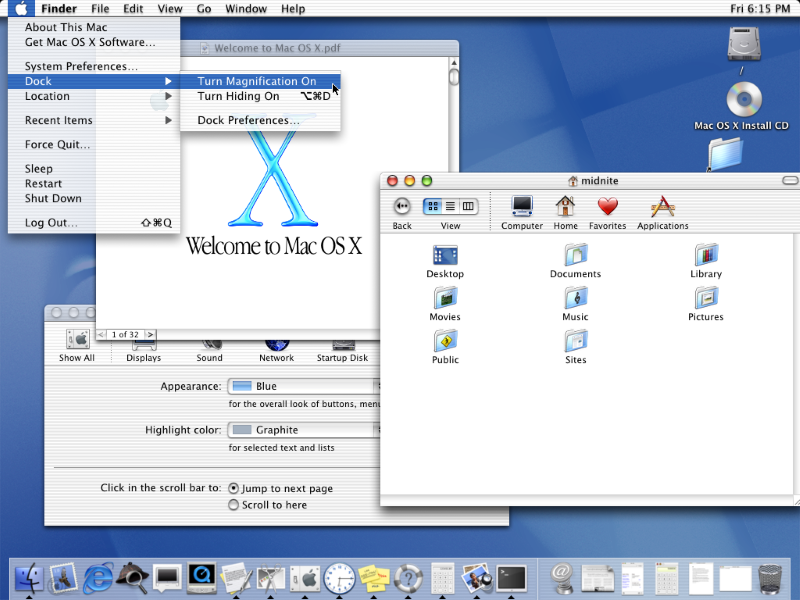
A few months later, Apple released OS X (10.1) named Puma. This iteration drastically improved system performance and began officially replacing Mac OS 9, OS X's predecessor, on all new computers shipped out.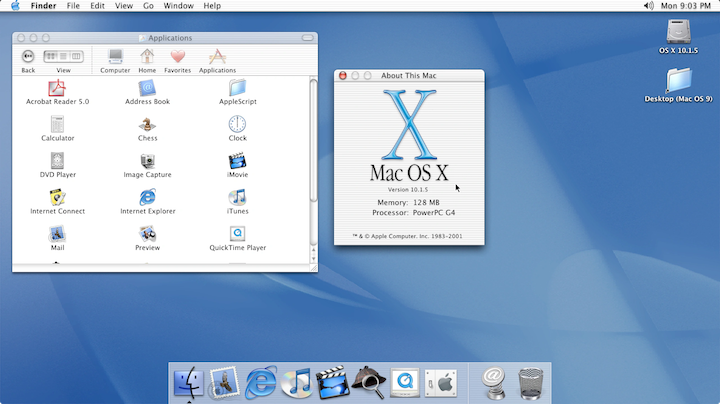
In the Fall of 2002, the next iteration of OS X was released. OS X (10.2), named Jaguar, focused on user interaction improvements and introduced new applications like iChat to the world.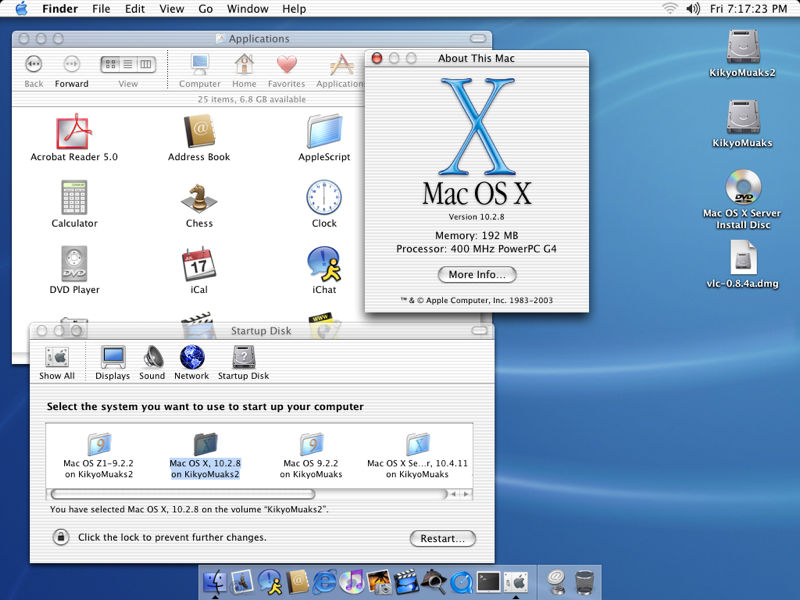
2003
OS X (10.3) named Panther was released in the fall of 2003. Most interesting about this release
was the fact that Apple's new web browser Safari replaced Internet Explorer on their hosts. Support for
integration with Active Directory was also added during this release.

2005
OS X (10.4) named Tiger released, bringing with it new features and new looks with Widgets and
dashboards. Up to this point, only PowerPC processors were supported for Apple products. With this release, Apple
hit a milestone by officially releasing support for the Intel based chipset in their hosts.
2007-2009
2007 was a big year for Apple. In the spring, they unveiled their new gadget that changed the world, the
iPhone and with it iOS, which was completely based on Mac OS X. That same year in the fall, OS X (10.5) Leopard was released and
introduced Apple's built-in backup system, Time Machine, along with support for 64-bit applications. At this
point, dual-booting was first introduced to the Mac line with the introduction of Boot Camp, providing support
for the Windows OS on Mac hardware.
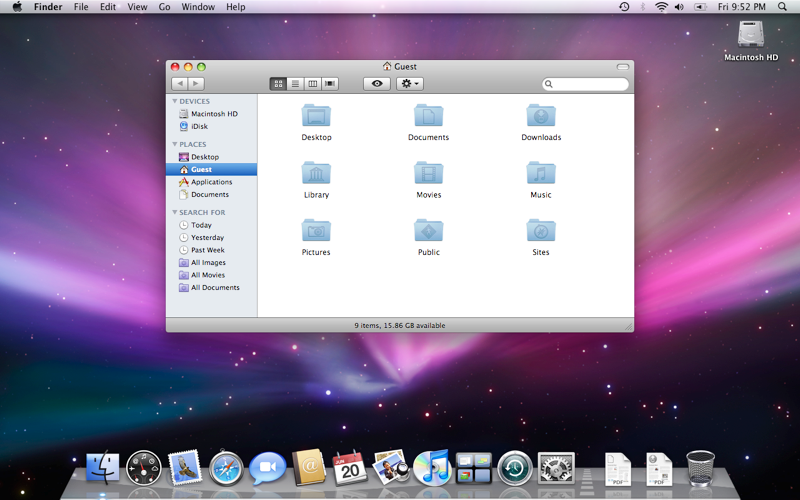
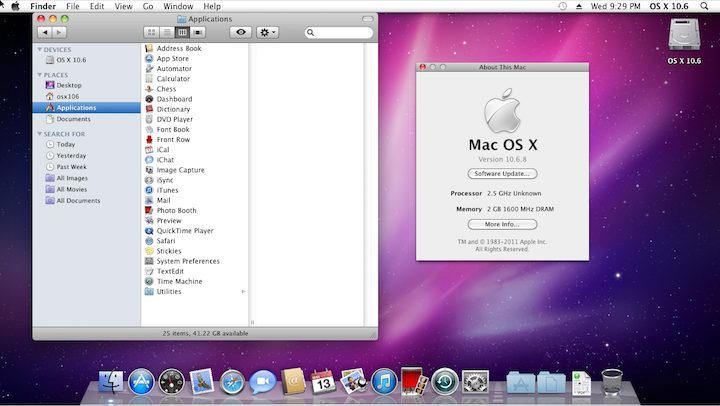
Following Leopard in 2009, OS X (10.6) Snow Leopard released,
which was an incremental update over Leopard. The only real changes were the addition of the AppStore and the discontinuation of support for the PowerPC processors. From this point on, Apple moved to Intel
based processors exclusively.
2011-2012
OS X (10.7) Lion brought many successful features from iOS to their Mac OS X, like Gestures and
saved window states. Lion also saw the introduction of iCloud to Mac OS X, bringing
interconnected cloud storage to the Apple realm of products.

2012 brought us Mountain Lion (10.8),
with the main focus on bringing many of the features that were currently iOS-only into Mac OS X. 
2013
From this point
forward, Apple decided to stick to a yearly release cycle of Mac OS X. After over a decade of releases named after big wild
cats, Apple also decided to ditch the animal theme and move to a naming convention based off locations and landmarks
within California.. With a fresh new naming standard, OS X (10.9) Mavericks, kicks off the new release schedule and
Apple put out a statement that all future releases would be free for upgrade (including this one).
There were some functionality tweaks but nothing substantial under the hood.
2014-2015
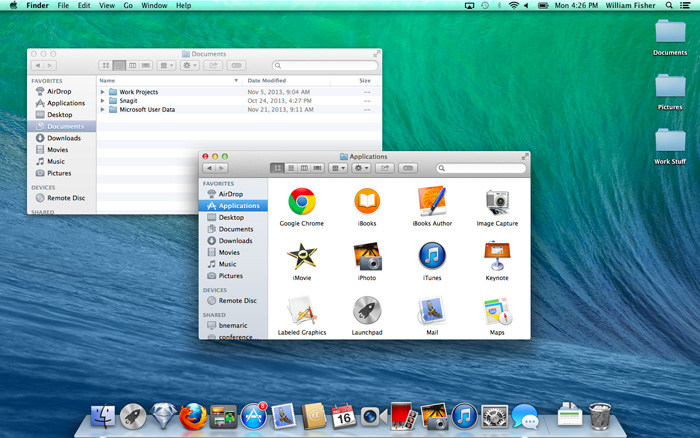
With the release of OS X (10.10) Yosemite, the Handoff functionality brought exciting change to the
Apple product lines allowing users to seamlessly move any task users are working on from one Apple device to another.
The UI is moving more toward the iOS look and feel.

OS X (10.11) El Capitan brought more
performance changes and the ability to tile your screen with split views.

2016-2017
OS X is dead! Long live macOS. With the release of macOS (10.12) named Sierra, Apple
officially moved away from the "OS X" moniker to "macOS". Along with this change, Apple brought integration for
Siri, Apple Pay, and other tweaks under the hood to macOS.

macOS (10.13) High Sierra brought along
the switch to the Apple File System (APFS) and several other support functionalities under the
hood.

2018
macOS (10.14) Mojave brought significant visual enhancements with this update. Darkmode
was introduced to the platform, working natively with all macOS apps and many third-party ones. The ability to
have your host dynamically shift from dark mode to light mode with the time of day was also a big change. Mojave
also ported over several more iOS apps to macOS, like News, Stocks, and Home, to name a few.

2019
macOS (10.15) Catalina split iTunes into three separate apps (Apple TV, Podcasts,
and Music). This update also focused on bringing more iOS features to macOS and also allowed the use of an
iPad as a secondary display with the Sidecar feature.

2020
macOS 11 releases, named Big Sur, finally moved away from OS version 10 (or X) and brought big changes to the UI and functionality of the OS
as a whole. Much care was taken to improve communications channels in this revision as well. The major new feature of macOS 11 was supporting the all-new Apple Silicon processor while still supporting Intel processors for at least a few more years. Much of the focus of this
revision also went to bug fixes.

2021
macOS 12 Monterey. Integration improvements, dubbed Universal Control, were introduced
that made controlling multiple Apple devices at once much more seamless. AirPlay saw some big changes, and you
can now use a Mac as a speaker when casting to other devices. Spatial Audio was introduced to
Facetime, along with other features like SharePlay which, allow you to share audio, video, and even your screen
with other users over FaceTime.
2022
macOS 13 Ventura is the most recent release of macOS as of the time of writing this module. It
introduced a new window management feature called Stage Manager, along with other features like
Continuity Camera, new Apps and app updates, a facelift to the settings app, along with other
features.

Now that we know a bit about the history of macOS let's dive into the architecture of the OS itself and some of its core components.
OS & Architecture Info
Kernel: XNU
- The Mach kernel is the basis (along with portions from BSD) of the macOS and iOS
XNUKernel architecture, which handles our memory, processors, drivers, and other low-level processes.
OS Base: Darwin, a FreeBSD Derivative open-sourced by Apple.
- Darwin is the base of the macOS operating system. Apple has released Darwin for open-source use. Darwin, combined with several other components such as
Aqua,Finder, and othercustom components, make up the macOS as we know it.
As mentioned above, macOS recently shifted to mainly support Apple Silicon while still supporting Intel processors for the time being.
These points above make up the basis of macOS as an operating system. There is much more to it, but we are just trying to get an initial understanding of what macOS is for now. Next, let us address several core components within macOS.
Core Components
GUI: Aqua is the basis for the Graphical interface and visual theme for macOS. As technology has advanced, so has Aqua, providing more and more support for other displays, rendering technologies, and much more. It is known for its flowy style, animations, and transparency with windows and taskbars.
File Manager: Finder is the component of macOS that provides the Desktop experience and File management functions within the OS. Aqua is also responsible for the launching of other applications.
Application Sandbox: By default, macOS and any apps within it utilize the concept of sandboxing, which restricts the application's access outside of the resources necessary for it to run. This security feature would limit the risk of a vulnerability to the application itself and prevent harm to the macOS system or other files/applications within it.
Cocoa: Cocoa is the application management layer and API used with macOS. It is responsible for the behavior of many built-in applications within macOS. Cocoa is also a development framework made for bringing applications into the Apple ecosystem. Things like notifications, Siri, and more, function because of Cocoa.
Now that we have a general idea of what macOS is, its origins, and what it is comprised of, let's move on to explore the user interface and all it entails.