Summary
In this module, we'll show you how to test the security limits of some of the most well-known and used authentication techniques.
We will cover the following:
- What is authentication
- Techniques to identify authentication-related issues (OAuth, SSO, Tokens)
- Explaining multiple types of related vulnerabilities
Additionally, you will also learn the following:
-
JWT (JSON Web Token)
- What is JWT
- JWT Flow
- No Verification of the signature
- None Algorithm Attack
- Brute Force Weak Secret
- Insecure KID Parameter Processing
-
OAuth
- What is OAuth
- OAuth Flow
- Account takeover via redirect_uri misconfiguration. (IDP)
- Account takeover via Open redirect (SP)
- Bruteforcing Weak Access Tokens
-
SAML
- What is SAML
- SAML flow
- Weak Public/Private Key Usage
- No Signature Verification
- Signature Stripping Attack
This module is broken into sections with accompanying hands-on exercises to practice the tactics and techniques we cover. The module ends with a practical hands-on skills assessment to gauge your understanding of the various topic areas.
As you work through the module, you will see example commands and command output for the topics introduced. It is worth reproducing as many of these examples as possible to reinforce further the concepts presented in each section. You can do this in the target host provided in the interactive sections or your virtual machine.
You can start and stop the module anytime and pick up where you left off. There is no time limit or "grading," but you must complete all of the exercises and the skills assessment to receive the maximum number of cubes and have this module marked as complete in any paths you have chosen.
The module is classified as "medium" and assumes an intermediate knowledge of how web applications function and common attack principles.
Introduction
Organizations want to streamline the user experience, allowing users to access multiple applications and websites by logging in only once. They may also want to reduce the number of disparate authentication and authorization silos for ease of management and to enforce standard policies.
Authentication and authorization frameworks such as OAuth and SAML can help organizations build secure and standard authentication and authorization flows.
What is Authentication
Authentication is the process of confirming a user’s identity or asking, "Are you who you claim to be?". An example of authentication is when you visit hackthebox.com and go to log in. The site asks you for your email and password then it'll confirm your credentials by matching them in the database (usually). If this fails, the site will return an error.
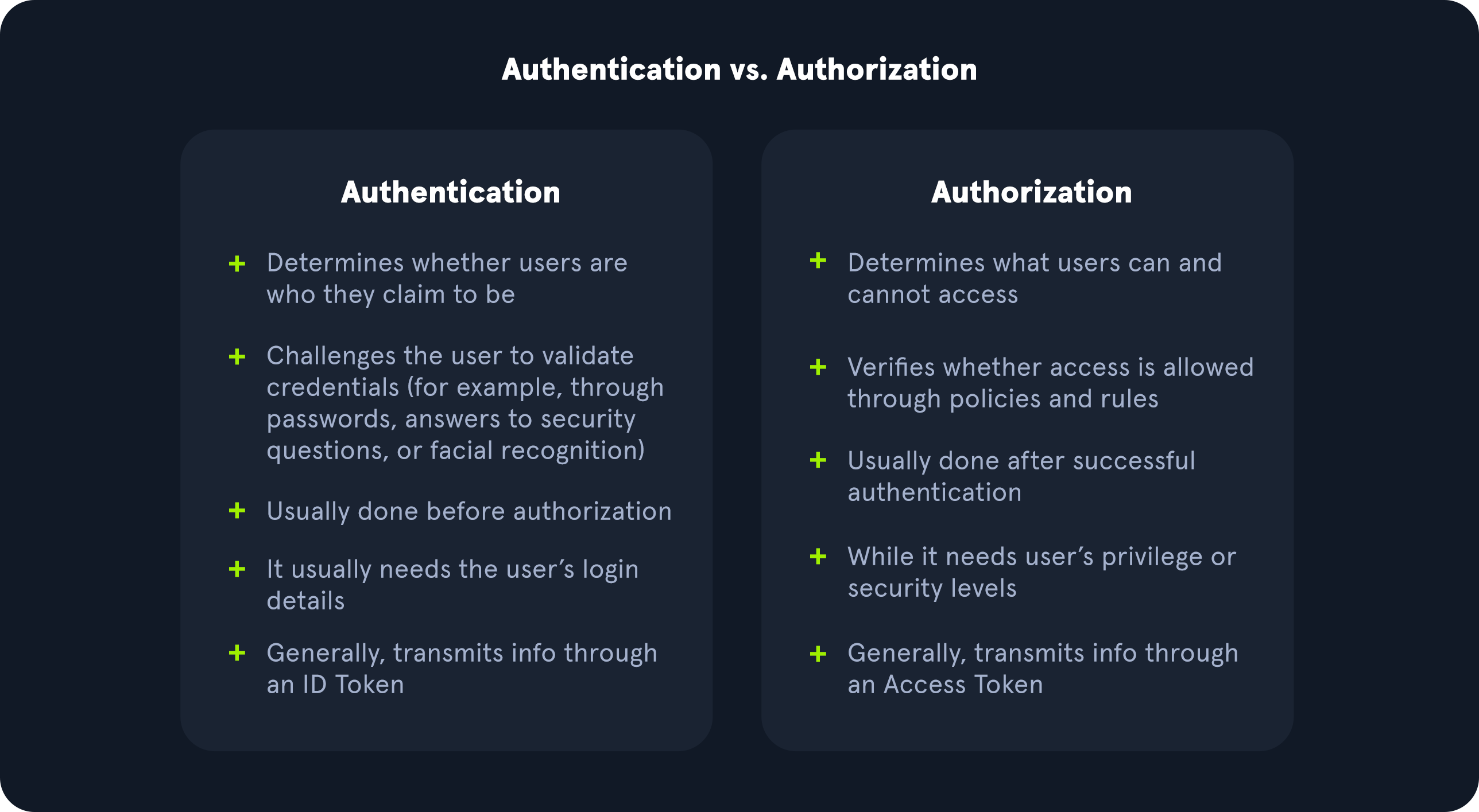
Authentication vs. Authorization
While Authentication verifies the user's identity, Authorization validates that they have access to the resources they are accessing, or asking, "Are you allowed to do/access this?". Unlike authentication, which we can interact with through login forms, authorization is usually handled on the backend, so attacking it requires a different perspective and techniques that assess how access control is handled in the web application. The graphic below shows some key differences between authentication and authorization.
Broken Authentication
It's not uncommon to find incorrectly implemented authentication mechanisms. The impact of this ranges from the disclosure of sensitive information to the compromise of the underlying OS. If we compromise an application's ability to identify the requesting user via its API, this compromises the overall web application security.
Authentication can be compromised in many ways, including:
- Brute-forcing the login page (credential stuffing) with a list of usernames and passwords.
- Manipulating unsigned or weakly signed session tokens such as JWT.
- Exploiting weak passwords and encryption keys.
- Obtaining authentication tokens and passwords from a URL.
The Broken Authentication module covered basic techniques to attack authentication mechanisms, and this module will focus on some of the more advanced authentication attacks.
JWT
A JSON Web Token (JWT) is an open standard used to create access tokens for an application. The JWT is created with a secret key that is private to the application. When an application receives a JWT from the user, it verifies that it was created with this secret key.
Any modification to the JWT without this key will result in verification failure. JWTs can be decoded as its encoded in base64 format. The JWT.io website can be used to decode a JWT.
In the upcoming sections, we will cover how the JWT authentication flow works and the multiple attacks that can be used to exploit it.
OAuth
Open Authorization (OAuth) is an open standard authorization framework. OAuth is used by platform applications and services, such as Google, Microsoft, GitHub, and Facebook, to provide delegated access to client applications using access tokens. In this way, an end user can access the client application without sharing their login credentials with the client.
OAuth can provide a large attack surface due to implementation flaws. Attacks on client applications can result in gaining access to confidential resources such as email (including email archives), communication and collaboration systems, and more. We will discuss OAuth flow in the upcoming sections and will cover multiple attacks to exploit it.
SAML
OAuth is not an authentication protocol. It effectively decouples a user's credentials from their requests to consumable resources. Instead, organizations may use LDAP (commonly Active Directory), Security Assertion Markup Language (SAML), or Central Authentication Service (CAS) to implement standard authentication schemes such as Single Sign On (SSO) for web applications. CAS is an open-source authentication protocol for implementing a standards-based single sign-on (SSO) for Web applications. It is one of many authentication protocols that can be integrated with authorization capabilities.
With SSO, a user logs into one application and can sign into other applications automatically, regardless of the domain the user is in or the technology in use. SAML implementations are often overlooked in most SSO applications due to the protocol's security. But there are some issues that may arise during the implementation of the SAML protocol.
Successful exploitation of SAML attacks results in authentication bypass, remote code execution, and unauthorized access to server resources, which we will cover in upcoming sections.



